The Chain of Trust: Why Biometrics Are Central to Secure Access Control
Published by Wanda Rich
Posted on February 23, 2022
5 min readLast updated: February 8, 2026
Add as preferred source on Google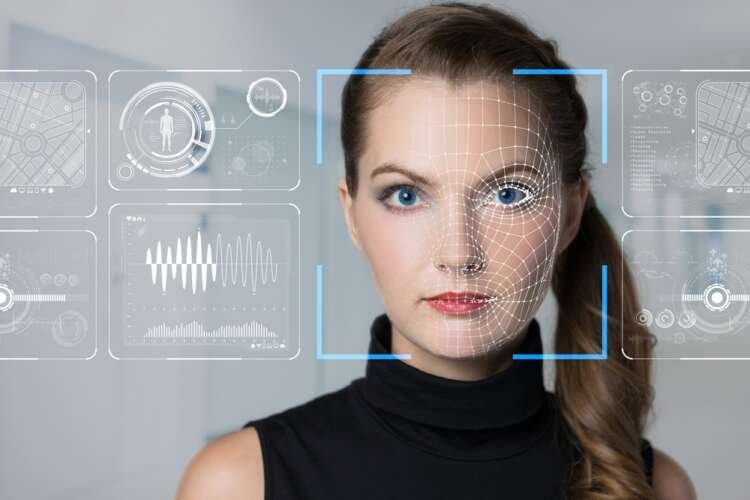
Published by Wanda Rich
Posted on February 23, 2022
5 min readLast updated: February 8, 2026
Add as preferred source on Google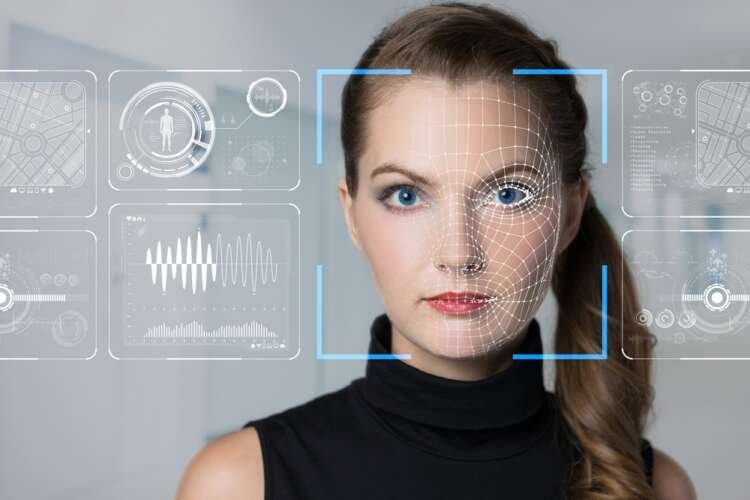
By Vince Graziani, CEO, IDEX Biometrics
Passwords simply aren’t secure enough in today’s digital world. With bots now able to try more than 100 billion password combinations per second, the average eight-character password can be cracked in as little as 12 minutes. Passwords have become the soft underbelly of the corporate network. According to Verizon’s 2021 Data Breach Investigations Report, three-in-five (61%) of all company data breaches last year involved stolen password credentials.
As work becomes hybrid and digital tools continue to hold an ever-stronger position in organisations, now is not a time to take chances. Since the launch of the EU’s General Data Protection Regulation (GDPR) in 2018, the Information Commissioners Office (ICO) has had the power to impose a fine on any businesses that falls foul of a data breach of €20m or 4% of annual turnover (whichever is greater).
Despite this, cyber-attackers are increasingly accessing corporate networks using weak, stolen, or otherwise compromised passwords. Traditional physical access to businesses is also much easier than many would care to admit and well within the wheelhouse of a motivated criminal. Key card duplicators that clone traditional RFID access cards have been around for a decade or more.
It’s not just in the traditional corporate realm where access to sensitive data is being breached daily. In the rapidly expanding world of cryptocurrency, fraud is widespread. Just this month saw the largest ever cryptocurrency hack, as a Blockchain bridge called Wormhole confirmed that roughly $320 million worth of Ethereum cryptocurrency was stolen.
Users of cryptocurrency store their funds on either hot or cold wallets. A ‘hot wallet’ is a device, such as a laptop or phone, connected to the internet. Convenient, but susceptible to digital currency heists of the kind seen this month. In contrast, a ‘cold wallet’ is external storage, like a hard drive or USB stick. A safer option from cyberhacks, but far less convenient. So users need a better solution – an accessible, security-assured ‘cold’ device .
With cyber-criminals attacking from every angle, it’s more important than ever for businesses and consumers alike to build a chain of trust: ensuring only the right people have access to the right devices, offices, and networks, at the right time. This is particularly important in high-risk industries, such as education, finance, healthcare and the public sector.
But how can you make sure that those that need to access your systems and offices can do so securely without impacting their daily lives? One of the answers lies in fingerprint biometric access.
The advancement of biometrics in logical and physical access
Many of us already use our fingerprint to access our mobile phone. It is proven access technology. At the Trustech event in Paris in December 2021, we saw several examples of how businesses are using fingerprint biometrics in the corporate world too. Dongwoon CEO Kim Dong Cheol was just one business leader who talked about a focus on innovative applications for card-based biometric authentication.
More companies are likely to embrace biometric fingerprint cards as part of their security systems in 2022. After all, biometric smart cards have numerous use cases. They give greater protection for many different security access areas of the modern business, whether that’s building access, logical authorisation on devices, or secure networks.
As the sector grows, fingerprint biometrics will surely be considered a standard approach to authentication, whether used in payment cards, digital wallets, or in digital ID applications.
The future of access control is right at our fingertips
The success of the Great Work From Home Experiment is largely due to increased usage of remote devices and acceleration of digital transformation. With reduced staff, hybrid working environments and the more remotely accessed digital tools comes growing security risks providing cybercriminals broader enterprise network exposure.
The recent trend for converged physical and logical access cards presents an ideal value proposition for on-card biometrics. Employee ID cards with integrated fingerprint authentication can now be used to manage non-transferrable employee access restricted to the individual.
These new generation smart access cards are enabled with both physical access protocols and mobile credentials that can be provisioned for instant onboarding or managed time-based access control. The combination of physical access protocols, provisionable user credentials and biometric identity management creates the next generation unified enterprise badge that will keep pace with the rapid increase in digital transformation. The chain of trust that fingerprint biometrics offers can be implemented to provide businesses and consumers with a far greater level of confidence in keeping their unified networks secure.
The importance of trust
While this is an excellent step forward for security, it is important that GDPR and data privacy requirements are always kept front and centre. It is also a case of trust. Both employees and consumers need to be comfortable with how their biometric data is used.
To do so, businesses should be fully transparent about their plans and procedures. That way, people know what to expect and understand the benefits of biometric access. These include enhanced convenience with better security, less to carry around and securely protected user biometric data that never leaves the card.
Biometric technology holds the key
With working from home realities continuing to accelerate digital transformation and device usage, the rate of data breaches continues to climb. To mitigate against the crippling impact and untold lost goodwill a breach can bring, it is crucial for businesses of all sizes to protect themselves against hackers. Cyberattack sophistication continues to rise and enterprises must act now to protect their offices, devices, and networks from attack.
Where passwords and legacy RFID access cards pose gaping security holes for businesses, innovations such as biometric technology hold the key to measurable and reliable access. By enabling the right employees to log in to their devices or access secure networks via their fingerprint, companies can markedly improve their security.
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks, ensuring the confidentiality, integrity, and availability of information.
A data breach occurs when unauthorized individuals gain access to sensitive, protected, or confidential data, often leading to data theft or exposure.
GDPR is a regulation in EU law on data protection and privacy, establishing guidelines for the collection and processing of personal information.
Access control is a security technique that regulates who or what can view or use resources in a computing environment, ensuring that only authorized users can gain access.
Explore more articles in the Technology category











