
Taming the Tiger in Your Network
Darren Turnbull, VP Strategic Solutions at Fortinet looks at how Smart Policies based on user ID or...
2nd July, 2013

Darren Turnbull, VP Strategic Solutions at Fortinet looks at how Smart Policies based on user ID or...
2nd July, 2013

Tips for handling security threats in the financial sector By Lior Arbel, CTO, Performanta Limited K...
2nd July, 2013

NTT Com Group, incorporating NTT Communications (NTT Com) and Integralis AG, a provider of global in...
28th June, 2013

RSA® Conference (www.rsaconference.com) the world’s leading information security conferences and exp...
26th June, 2013

by Andrew Millard, senior director marketing, EMEA, online services division at Citrix The deve...
19th June, 2013

ForeScout Recognised as the Largest Independent Vendor and the Fastest Growing Among Leaders in the...
19th June, 2013

Mapping and anticipating emerging threats can help inform crisis response but don’t be lulled into a...
18th June, 2013
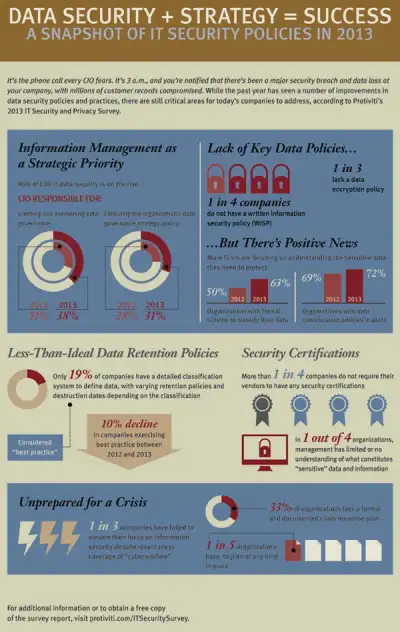
CIOs are assuming more strategic roles based on evolving risks and opportunities Despite broad recog...
14th June, 2013

“Did you close your bank accounts when $45 million were drained from ATMs in a cyber-heist earlier t...
14th June, 2013

Richard Blanford, Managing Director, Fordway The trend for individuals wanting to bring their own mo...
14th June, 2013

EMEA contributor Gary Newbold Regional Director Northern Europe, Extreme Networks Shadow IT is a mul...
13th June, 2013

Pat Phillips, practice director at independent IT and business change professional services firm Xce...
12th June, 2013