Q&A WITH PRAVIN KOTHARI, FOUNDER AND CEO OF CIPHERCLOUD
Published by Gbaf News
Posted on February 25, 2014
2 min readLast updated: January 22, 2026

Published by Gbaf News
Posted on February 25, 2014
2 min readLast updated: January 22, 2026

This will be the first “post-NSA” RSA conference, how have the Edward Snowden revelations changed the cybersecurity landscape?

Pravin Kothari CipherCloud
The Snowden revelations highlighted the extent of the government’s surveillance capabilities. This has driven three shifts:
Cloud, mobility and risk will dominate the RSA discussion. Are there other areas that the agenda missed?
A related issue is that of big data, which I see as both a cause for concern and as a security solution when used right. The more data an enterprise creates, shares and stores, the more burden it has to ensure security and compliance. However, as is the case with Splunk, HP ArcSight, my former company, and other log analytics companies, it is also possible to leverage big data to tighten security. As data bandwidths grow, more companies will need to leverage big data analytics.
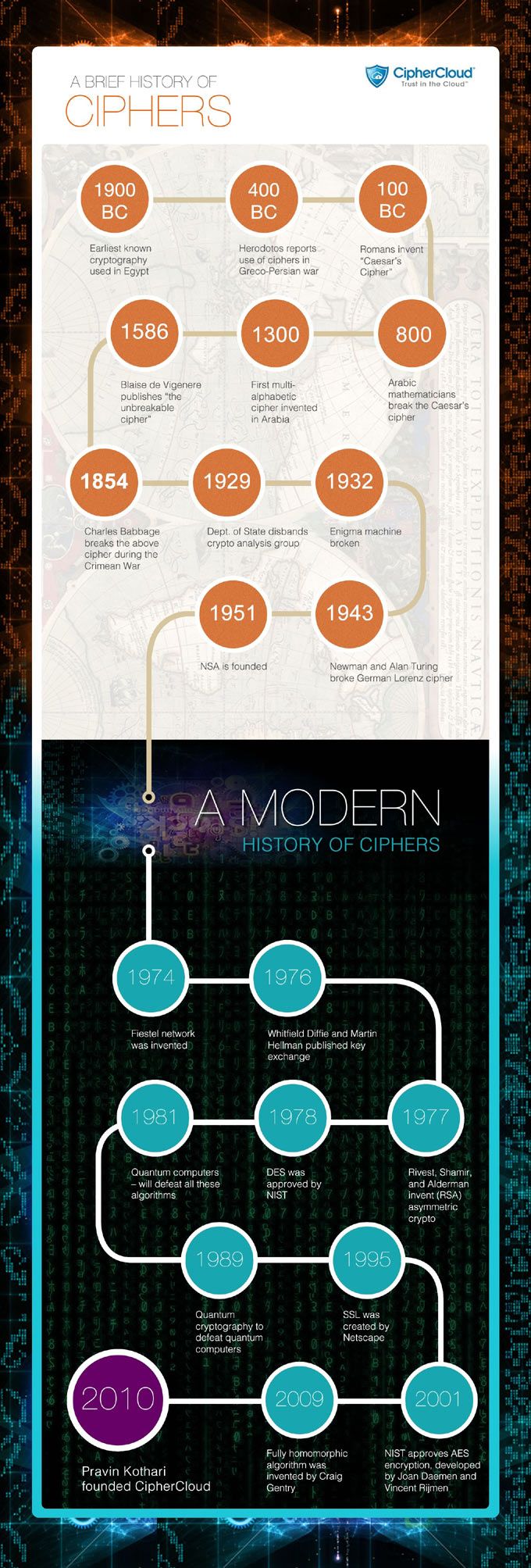
History of Encryption
Explore more articles in the Interviews category











