FINANCIAL INSTITUTIONS MUST HAVE A ‘DEFENSE IN DEPTH’ POSTURE TO SUCCESSFULLY COMBAT PAYMENTS FRAUD
Published by Gbaf News
Posted on June 3, 2014
5 min readLast updated: January 22, 2026
Published by Gbaf News
Posted on June 3, 2014
5 min readLast updated: January 22, 2026
Mike Urban, Director of Product Management, Financial Crime Risk Management, Fiserv.
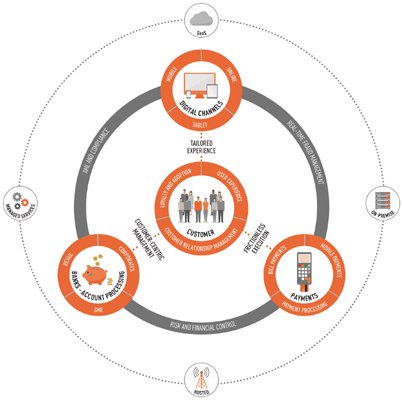
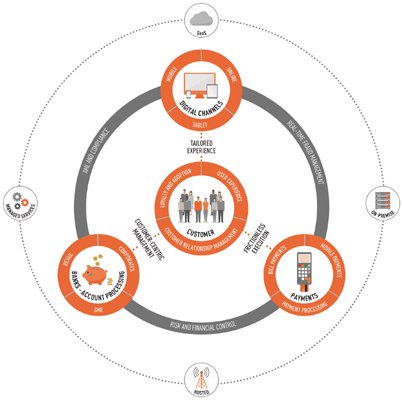
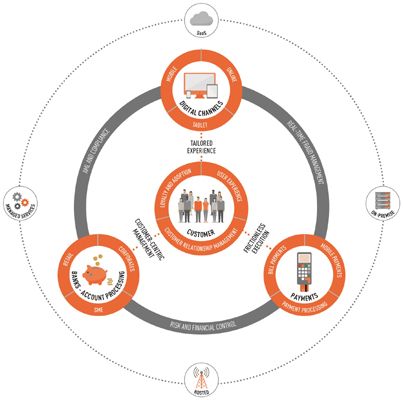
Electronic payments fraud is a constantly evolving and increasing threat, to both financial institutions and their clients. It encompasses all types of electronic financial transactions including wire and SEPA payments initiated from traditional channels as well as from mobile and tablet devices over digital channels. In recent years there has been a huge growth in consumer and business appetites for banking through digital channels, which started almost twenty years ago with online banking and now continues with mobile and tablet banking. As banks innovate in digital payments and add new channels and capabilities they must also ensure they have robust, interconnected back-end systems which enable digital channels, account and payments processing functions to communicate with each other in real time. A defense in depth model uses different controls at different points in the transaction to ensure that potentially fraudulent transactions are stopped.
All of the controls that institutions have in place for traditional banking infrastructures such as real-time fraud detection, anti-money laundering, compliance and reconciliation also need to be in place for the new world of mobile and digital payments. Criminals are devising increasingly complex and innovative ways to execute payments fraud so the creation of a robust prevention and detection strategy is imperative for financial institutions to protect both themselves and their clients. From a security perspective ensuring robust processes are in place which can detect and prevent malicious activity is crucial in order to maintain vital customer trust and can help institutions to gain competitive advantage against other financial institutions who fail to do this.
 Cybercriminals are becoming ever more sophisticated and varied in their attack methodologies. Malware is one of the most common methods to surreptitiously compromise computer systems and gain access to private information. Recent figures show that there are tens of millions of computer and mobile device malware variants and increasingly clever ways to deliver them. Spear phishing continues to be a very beneficial technique employed by criminals, professing to originate from a trusted source while gaining access to confidential data. Distributed Denial of Service (DDoS) attacks are executed not only by hactivist driven organizations, they are increasingly employed to divert the attention of bank security staff while criminals defraud their systems and clients. Criminals large and small also take advantage of financial institutions by placing insiders and bribing staff to steal funds and financial information.
Cybercriminals are becoming ever more sophisticated and varied in their attack methodologies. Malware is one of the most common methods to surreptitiously compromise computer systems and gain access to private information. Recent figures show that there are tens of millions of computer and mobile device malware variants and increasingly clever ways to deliver them. Spear phishing continues to be a very beneficial technique employed by criminals, professing to originate from a trusted source while gaining access to confidential data. Distributed Denial of Service (DDoS) attacks are executed not only by hactivist driven organizations, they are increasingly employed to divert the attention of bank security staff while criminals defraud their systems and clients. Criminals large and small also take advantage of financial institutions by placing insiders and bribing staff to steal funds and financial information.
A layered security model using different controls at different points in the transaction life cycle means that a gap in one control is closed by another control. Layers should include:
Perimeter Detection – monitors whether an attempt to access an account on a particular device is consistent with previous behavior
Transaction Initiation – uses behavioral profiling to determine whether the type of transaction is consistent with previous transactions, or consistent with the behavior of a peer customer or business.
Transaction Authentication – uses multifactor authentication and identification. Non-transactional data is used to authorise a transaction at this stage and financial crime platforms use predictive modelling based on outcomes of previous investigations to flag whether a transaction is potentially fraudulent
The ability to adapt these controls in real time based on information and patterns enables financial institutions to maintain a ‘defense in depth’ posture.
Consider this scenario: the latest tablet app is used to initiate an unusually large wire transfer on a commercial client’s account to a new counterparty in a foreign jurisdiction. The layered security model can help an institution tell if this is a legitimate transaction, or something more sinister. Before that message completes (or even begins) its journey, the financial institution needs to address a growing myriad of security and integrity risks, ranging from identity theft and internal fraud to money laundering and sanctions violations.
The stage at which an institutions’ financial crime prevention and detection systems will flag a transaction as suspicious depends on the risk profile of the individual or organisation involved. The defences that financial institutions have in place need to be configurable and flexible enough to rapidly react to evolving typologies of financial crime and threats as they occur. Financial institutions must be empowered to effect changes themselves to minimize exposure as the risk environment changes.
The growing use of the mobile channel for banking transactions creates its own unique set of challenges. Global mobile banking users are set to exceed 1 billion by 2017, but while there is great demand for these services, consumers are also fearful of the risks associated with mobile banking such as cybercrime and fraud. Mobile devices are an additional entry point for criminals to commit payments fraud. However, financial institutions can learn to leverage the additional information and characteristics available in mobile devices and mobile apps to enhance risk signals. These signals can also be used to understand the risks associated with other transactions channels, such as comparing the location of the phone with the merchant address of a POS terminal.
Consumers often store personal data on their devices, such as social network accounts that they are permanently logged into. According to the 2012 Identity Fraud Report, ‘Social Media and Mobile Forming the New Fraud Frontier’ which Fiserv co-sponsored, only 38% of smartphone owners and 34% of tablet owners use passwords on their home screens. The report also revealed that one third of smartphone owners save personal login data to their device, making it very easy for criminals to steal their details to use fraudulently.
Having a defense in depth mindset enables financial institutions to keep up with criminals and the regulators, as wellasthe fast moving innovation in digital channels and (payment) infrastructures. There is a balance that must be struck in order to ensure customer account security while still allowing for innovation across channels. The key is strong communication between digital channels, account processing and payments processing, ensuring that these areas of the business are always communicating with others in order to flag potentially fraudulent activity before the transaction is completed.
Explore more articles in the Technology category











